Is Microsoft 365 Account Hacked? Know What to Do!

As our lives become increasingly digital, dependence on services like Office 365 is all but mandatory. Whether it is used in an individual capacity or for business productivity, security can’t be taken lightly. Thus, when a situation like a Microsoft 365 account hacked occurs, it is cause for concern.
A compromised account is when someone other than the owner has access to a particular account. Credentials like passwords, passcodes, security pins, etc control the right to view and use a service. When these fall into the wrong hands due to data leaks or security malpractice, users must deal with the situation ASAP.
Therefore, to assist users, we’ve gathered information from trusted sources and incorporated expert insights too. Which together form a clear pathway to provide you with actionable steps for safeguarding your Microsoft 365 account.
Consider a Scenario:
A new member in an organization unaware of the security protocols received a welcome mail containing a link. The user clicked on the link without thinking much to open it, but no apparent changes were visible. However, unknowingly, the member became a victim of a scam.
Now, the attackers targeted & used Office 365 vulnerabilities to obtain the password of that account. After this, they started performing illegal activities such as sending spam emails to other users. This is the most clear-cut case of an Office 365 account hacked/compromised via a cyber-crime. Now, that member of an organization wants to fix this issue so that it stops affecting the organization data stored in an Office 365 account.
How to Verify if an Office 365 User Mailbox is Compromised?
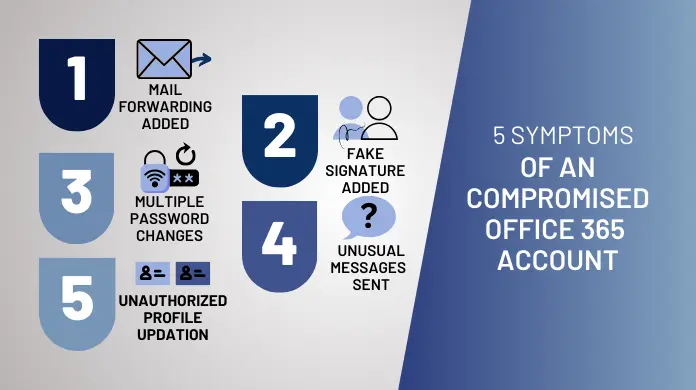
There are various reasons through which a user can confirm that the Microsoft O365 account has been compromised or not. All of them are listed below:
- A user is not able to sign in to an Office 365 account through his usual password.
- There are changes in the profile, such as the name, postal code, or phone number not done by the user.
- The deleted or sent items folders contain hacked-account messages.
- A new signature was recently added, such as a prescription drug signature, etc.
- The same Office 365 account sent multiple credential-change requests in a short period.
- Emails in bulk have been sent from your account that contain invalid email addresses.
- If you consider your Microsoft 365 account hacked, look for inappropriate messages sent at odd hours. Like:
-
- Requesting money from colleagues.
- Asking contacts to invest in a third-party scheme.
- Sending fake job applications on behalf of the company
-
- There might be chunks of mail history missing all of a sudden.
A hacked account is bound to increase Office 365 migration challenges as well so it becomes even more important to resolve this problem.
If any Office 365 user encounters this common problem in their account then, it means the Office 365 account has been compromised or hacked by someone and needs to be fixed as soon as possible.
How to Resolve Microsoft 365 Account Hacked Issue
In case the compromise is limited to the user level the admin can still log in from their end and restore functionality. However, if in a worst-case scenario the admin account itself is the victim then the following methods may or may not work.
To resolve the hacking problem in the Office 365 account, there are two methods available for use. A user can choose any of them.
Method 1: Remediate Compromised Account Via GUI
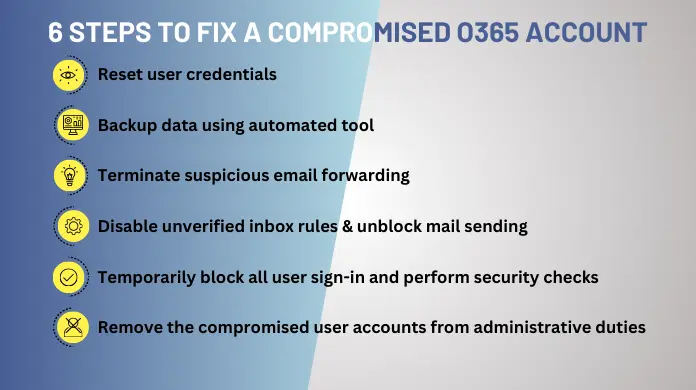
There are various manual redemption methods available that a user can try to fix the Office 365 account compromised/ hacked problem. Let’s look at the steps one by one:
- Update Office 365 Account Password- By updating the user password, a user not only modifies the password to secure the account, moreover it also ends all active sessions that are currently active.
- Back up and Store all Critical Data Locally- to overcome such type situations, it is always suggested to regularly back up your Office 365 data. If a user has an Office account backup on their local machine then users have the option to close the hacked account permanently and reload the data on a new account.
- Disable Mail Forwarding to Feature- A user must disable the rules of mail forwarding to external domains and global mail forwarding rules that are mainly generated by an attacker.
- Reviewing and Disabling Mailbox Rules- Hackers commonly implement rules to disrupt mail flow. So admins must take steps to prevent further misuse of business resources.
- Pause User Login and Logout Activity- When the passwords are reset, the hacker may attempt to log in again. So to prevent this admin must take proactive steps.
- Removing the Account from Administrator Roles- Treat all admin-level accounts as potential threats unless otherwise. In the event an attacker gains admin access, they can exploit various aspects of the entire Microsoft 365 tenant, posing significant risks.
Method 2: Execute RemediateBreachedAccounts.ps1 Script of PowerShell for Hacked Office 365 Account
This PowerShell script will help resolve the issue of the Office 365 account hacked. It works by restoring the compromised account and performing all the above-stated actions in method 1 automatically using this RemediateBreachedAccounts.ps1 Script.
Best Practices to Prevent Compromised Accounts in the Future
- Set up A Multi-Factor Authentication (MFA) System
Multi-factor authentication adds a security layer on top of the already existing password. Here user makes use of secondary features such as phone number, biometrics, and authenticator apps to validate their identity.
It is similar to how banks ask for OTP during a transaction. An organization can use any of the verified systems or even design custom solutions for MFA.
Once you set up MultiFactor Authentication, cybercriminals can’t access the account even if they break the password. Therefore, it reduces the risk of any external entity hacking an Office 365 account.
- Avoid Getting Microsoft 365 Account Hacked Issue by Tweaking the Password Policy
A user must configure the account with a strong password that has a high level of complexity. While setting up the password policy the admin should consider the following points:- Keep the password length a minimum of 10 characters
- Avoid using common words and names
- Combine numbers and symbols to make it harder to break via brute force attack
Moreover, one must also set a password expiration policy, this is to provide a safety net against password leaks, it also prevents a disgruntled employee from trying to misuse their old credentials.
Sometimes certain employees in critical roles may turn off MFA voluntarily (like a break-glass global Office 365 admin role in an Organization). In such cases, a strong password is the only line of defense against nefarious entities.
- Review the Audit Log and Enable Mailbox Auditing
Enabling mailbox auditing will enable users to monitor the activity and also allow them to identify any anomalous activity in their mailbox. - Security Education and Awareness
In today’s world, where cyber crimes are increasing day by day it becomes necessary to educate the users about security threats like ransomware and spear-phishing.
Conclusion
Through this guide, we found the steps to take in the aftermath of a Microsoft 365 account hacked suspicion. We analyzed the symptoms that are common to all Office 365 accounts compromised via a cyberattack. As these attacks become ever increasing organizations must plan accordingly.
One of the steps in this preparation is to take a backup of all critical data from time to time. Admins can then store the data on a local device that is independent of the internet. We also provided a script for those looking for a more technical-oriented solution.
Frequently Asked Questions
Q. What steps should I take if I think my Microsoft 365 account has been compromised?
Immediately, update your password, activate multi-factor authentication (MFA), and check your account settings for any suspicious alterations.
Q. How can I protect my Microsoft 365 account from phishing attacks?
Be cautious with emails asking for personal information, verify the sender’s identity, avoid clicking on suspicious links, and report phishing attempts to your IT department.
Q. What steps should I take if I observe apps that I don’t recognize linked to my Microsoft 365 account?
Revoke access to these apps right away via the account security options and examine the permissions allowed by any apps that are still connected.
Q. Is it possible to set up alerts for suspicious activities in Microsoft 365?
Yes, you can set up activity alerts in the Security & Compliance Center to receive notifications for unusual or suspicious activities.